The source code can be found here
https://github.com/jimmysyss/google-drive-backup
I have looking for offsite backup solution for my VPS, the are plenty of paid solutions, however, it will be perfect if we can leverage something like Google Drive and Dropbox. I use Google Drive for the time being.
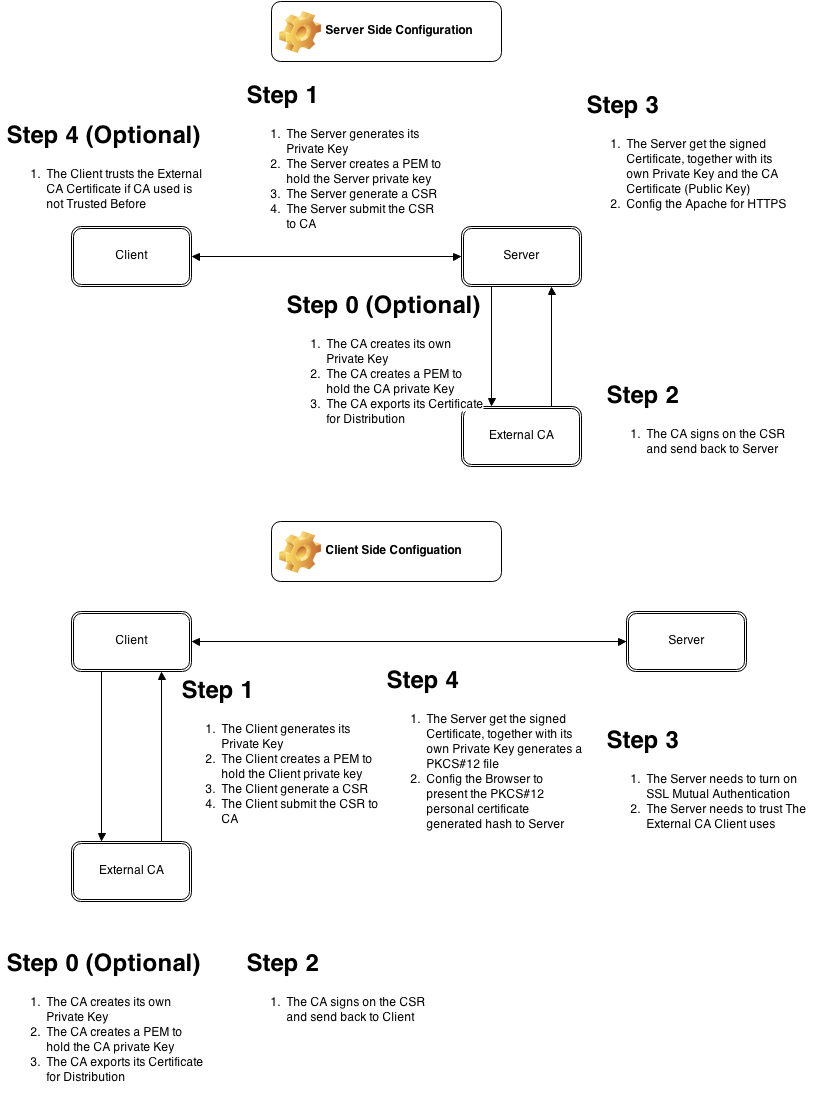
It is a two steps process. First is obtained an OAuth Authentication from Google API. Second is using the Google Drive API to upload a file.
OAuth API
Google OAuth API
Google Drive API
Google Drive API
There are two script in my Github, the first one is helping you to get the credential and save it in a file (Storage), It is a one off process. The second step is using the credential you got and submit the file to Google Drive.
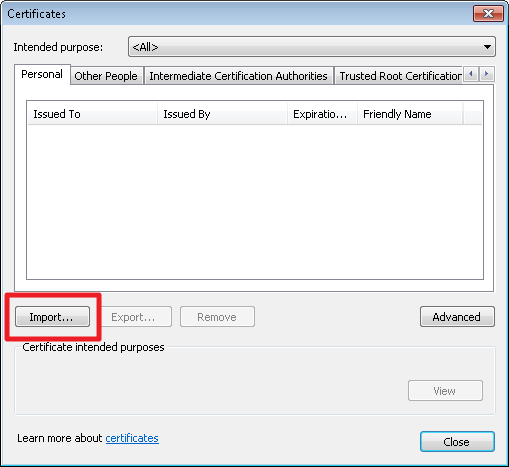
For the GetCredential.py, you need to a new Application Secret from you Google Developers Console => Authentication Page. You need to select Create Client ID => Installed Application => Other (NOT IOS / Android). And then download the JSON file and place at the same directory as the python file.
Next, you run the python file with the following syntax. CLIENTSECRET_PATH is the JSON file in previous step. SAVE_STORAGE_NAME is the new Credential Storage file. Follow the steps in script to get the Application Authenticated ID
./GetCredential.py CLIENTSECRET_PATH SAVE_STORAGE_NAME
After you get the SAVE_STORAGE_NAME file, you can use it to upload the file, you don’t need to get a new SAVE_STORAGE_NAME every time, it will handle the OAuth Key Exchange for you. The command is as followed. FULL_FILENAME is the path to file you want to upload.
UploadToGoogle.py STORAGE_FILE FULL_FILENAME
There are couples of vocabulary that help you to understand how the application runs.
Client ID and Client Secret: Google ID for your APPLICATION, not the User Identity. In OAuth, the Client ID is used to generate a URL for user to authenticate.
Credential: the application logic that help you to add application header to your HTTP Clients.
Storage: The media, either DB or File to store the credential, which can be reused later on. Furthermore, it also helps to handle the Renew of the Token.
Enjoy!
^_^